This work introduces two algebraic variants of the Massey-Omura cryptosystem based on newly defined generalized (k,t)-Jacobsthal p-numbers and their extensions to finite groups. We first generalize the classical Jacobsthal recurrence and establish structural properties including periodicity, invertibility conditions, and recurrence behavior modulo finite integers. These results are then extended to group-theoretic settings, where we construct the corresponding (k,t)-Jacobsthal sequences in specific finite groups and derive their sequence periods. Leveraging these algebraic foundations, we propose two Massey-Omura-type encryption schemes in which private exponents are selected from the generalized Jacobsthal sequences. We formally prove the correctness of both constructions and analyze the implications of periodicity on exponent invertibility and protocol feasibility. The proposed schemes do not introduce new hardness assumptions beyond those inherent in the underlying platform group. Instead, they provide a mathematically structured alternative to classical exponent selection in three-pass protocols. The results highlight a new connection between recurrence-defined sequences and multiplicative exponentiation in finite groups, offering an algebraically motivated direction for exploring generalized exponent families in symmetric and non-abelian cryptosystems.
Cryptography plays a central role in securing modern communication systems, enabling confidentiality, authenticity, and integrity in the presence of adversaries with increasing computational capabilities. Many cryptographic constructions, both classical and modern, draw deeply on algebraic structures, including number-theoretic sequences, finite fields, and groups. Recurrence-defined sequences such as the Fibonacci, Pell, and Jacobsthal numbers have been used in pseudorandom number generation, key-scheduling mechanisms, algebraic code constructions, and various symmetric and asymmetric schemes. Their predictable recurrence relations and well-defined behavior modulo integers or within finite groups make them attractive for both theoretical study and potential cryptographic applications.
The Jacobsthal sequence \(\lbrace J_n\rbrace\) is defined as \[\begin{aligned} \nonumber J_n=J_{n-1}+2J_{n-2},~ n\geq 2, \end{aligned}\] with initial conditions \(J_0=0\) and \(J_1=1\) [17]. In 2008, the Jacobsthal Lucas \(E\)-matrix and \(R\)-matrix were given which are similar to the Fibonacci \(Q\)-matrix [18]. In [3], Gaussian Jacobsthal sequences were introduced and the corresponding generating functions were given. Generalized Jacobsthal sequences were introduced in [10] and the \(k-\)Jacobstal sequences in [27]. In [1], the Jacobsthal-Padovan \(p\)-sequences in finite groups were presented, and the orbits of these groups were given.
The Jacobsthal numbers have been generalized in several ways [6, 7]. One of these generalizations is as follows. For \(n\geq 0\) and \(k \geq 2\), the generalized Jacobsthal sequence \(J(k,n)\) is defined as \[\begin{aligned} J(k,n) = (k – 1)J(k, n-1) + kJ(k, n- 2) \mbox{ for } n \geq 2, \end{aligned}\] with initial conditions \(J(k, 0) = 0\) and \(J(k, 1) = 1\) [5]. For example, if \(k=2\), we have \[\begin{aligned} J(2,n) = J(2, n-1)+ 2J(2, n- 2)~ for ~n \geq 2, \end{aligned}\] and thus \(\lbrace J(2,n)\rbrace_0^\infty=\lbrace 0, 1, 1, 3, 5, \cdots \rbrace\).
Algebra, in particular group algebra, plays an important role in modern encryption. The properties of groups and rings have been used to create public and private keys [4, 13, 20, 21, 24, 23]. In 1986, the Massey-Omura cryptosystem was introduced [19]. It has become one of the most well-known private key cryptosystems [2, 11, 28]. In [26], a Massey-Omura cryptosystem was developed in \(GF(2^m)\). The Massey-Omura algorithm was used for a three-pass protocol in [25]. In [12], Massey-Omura encryption was considered using symmetric groups.
In this paper, we define the generalized \((k,t)\)-Jacobsthal \(p\)-numbers, analyze their modular periodic behavior, and then extend the construction to selected finite groups. The resulting algebraic framework is used to build two Massey–Omura-type protocols in which the private exponents are chosen from recurrence-defined families rather than from unrestricted residue classes. Our aim is not to claim a stronger cryptosystem than the classical Massey–Omura scheme, but to study how structured exponent families interact with correctness, invertibility, and effective keyspace in finite-group settings.
The remainder of this paper is organized as follows. Section 2 introduces the generalized Jacobsthal recurrence and studies its modular behavior. Section 3 defines the corresponding sequences in finite groups and specializes them to \(G_m\) and \(H_{(t,l,m)}\). Section 4 presents two Massey–Omura-type constructions based on these sequences, and Section 5 discusses their scope, limitations, and keyspace implications. Finally, Section 6 summarizes the main conclusions and possible extensions.
In this section, we introduce the generalized \((k,t)\)-Jacobsthal \(p\)-numbers and study their modular recurrence properties. We first record the defining recurrence and then examine the periodic behavior that arises after reduction modulo a positive integer. These results will be used later in the group-theoretic and cryptographic constructions.
Definition 2.1. For integers \(k\geq 1\), \(p \geq 1\) and \(t\geq 2\), the generalized \((k,t)\)-Jacobsthal \(p-\)numbers denoted \(\lbrace J_n^p(k,t)\rbrace\) are defined as \[\begin{aligned} J_n^p(k,t)=kJ_{n-1}^p(k,t)+2J_{n-p-1}^p(k,t)+J_{n-p-2}^p(k,t)+\cdots+J_{n-p- t}^p(k,t),~ n\geq t+p+1, \end{aligned} \tag{1}\] where \(J_0^p(k,t)=J_1^p(k,t)=\dots=J_{t+p-1}^p(k,t)=0\) and \(J_{t+p}^p(k,t)=1\).
Note that Definition 2.1 can be rewritten as \[\begin{aligned} J_n^p(k,t)=kJ_{n-1}^p(k,t)+2J_{n-p-1}^p(k,t)+\sum_{r=2}^tJ_{n-p-r}^p(k,t),~ n\geq t+p+1. \end{aligned} \tag{2}\]
For example, if \(p=1\) and \(k=3\), from Definition 2.1 we have \[\begin{aligned} J_n^1(3,t)=3J_{n-1}^1(3,t)+2J_{n-2}^1(3,t)+\cdots+J_{n-1- t}^1(3,t),~ n\geq t+1. \end{aligned} \tag{3}\]
Table 1 gives \(J_n^1(3,t)\), for \(0\leq n \leq 10\) and \(2 \leq t \leq 8\).
The generalized \((k,t)\)-Jacobsthal \(p\)-numbers modulo \(m\) are \[\lbrace J_i^{p,m}(k,t) \rbrace= \lbrace J_0^{p,m}(k,t), J_1^{p,m}(k,t), \cdots, J_n^{p,m}(k,t), \cdots \rbrace,\] where \(i \geq 0\) and \(J_i^{p,m}(k,t)\equiv J_i^p(k,t) \ (\mathrm{mod}\ m)\).
Theorem 2.2. For \(t\geq 2\), the generalized \((k,t)\)-Jacobsthal \(p\)-numbers \(\lbrace J_n^{p,m}(k,t) \rbrace\) are eventually periodic modulo \(m\).
Proof. Consider the state vector \[S_n:=(J_{n}^{p,m}(k,t),J_{n+1}^{p,m}(k,t),\cdots, J_{n+t+p-1}^{p,m}(k,t))\in \mathbb{Z}_m^{t+p}.\] Because the recurrence in Definition 2.1 depends only on the previous \(t+p\) terms, the state vector \(S_n\) uniquely determines the next value \(J_{n+t+p}^{p,m}(k,t)\) and hence the next state vector \[S_{n+1}:=(J_{n+1}^{p,m}(k,t),J_{n+2}^{p,m}(k,t),\cdots, J_{n+t+p}^{p,m}(k,t)).\] Thus the sequence of states evolves under a deterministic map \[S_{n+1}=F(S_n),\] for some function \(F:\mathbb{Z}_m^{t+p}\longrightarrow \mathbb{Z}_m^{t+p}\). Since each coordinate of \(S_n\) lies in \(\mathbb{Z}_m\), there are only \(m^{t+p}\) possible state vectors. Therefore the infinite sequence \(S_0,S_1,S_2,\ldots\) must contain a repeated state, say \(S_i=S_j\) with \(0\leq i<j\). By determinism, this implies \(S_{i+r}=S_{j+r}\) for every \(r\geq 0\). Hence the state sequence is periodic from index \(i\) onward, and the original scalar sequence \(\lbrace J_n^{p,m}(k,t)\rbrace\) is eventually periodic modulo \(m\). ◻
| \(n\) | \(J_n^1(3,2)\) | \(J_n^1(3,3)\) | \(h J_n^1(3, 4)\) | \(J_n^1(3,5)\) | \(J_n^1(3,6)\) | \(J_n^1(3,7)\) | \(J_n^1(3,8)\) |
|---|---|---|---|---|---|---|---|
| \(0\) | \(0\) | \(0\) | \(0\) | \(0\) | \(0\) | \(0\) | \(0\) |
| \(1\) | \(0\) | \(0\) | \(0\) | \(0\) | \(0\) | \(0\) | \(0\) |
| \(2\) | \(0\) | \(0\) | \(0\) | \(0\) | \(0\) | \(0\) | \(0\) |
| \(3\) | \(1\) | \(0\) | \(0\) | \(0\) | \(0\) | \(0\) | \(0\) |
| \(4\) | \(3\) | \(1\) | \(0\) | \(0\) | \(0\) | \(0\) | \(0\) |
| \(5\) | \(11\) | \(3\) | \(1\) | \(0\) | \(0\) | \(0\) | \(0\) |
| \(6\) | \(40\) | \(11\) | \(3\) | \(1\) | \(0\) | \(0\) | \(0\) |
| \(7\) | \(145\) | \(40\) | \(11\) | \(3\) | \(1\) | \(0\) | \(0\) |
| \(8\) | \(526\) | \(146\) | \(40\) | \(11\) | \(3\) | \(1\) | \(0\) |
| \(9\) | \(1903\) | \(532\) | \(146\) | \(40\) | \(11\) | \(3\) | \(1\) |
| \(10\) | \(6921\) | \(1939\) | \(533\) | \(146\) | \(40\) | \(11\) | \(3\) |
Whenever the initial state reappears, we write \(hJ_m^p(k,t)\) for the least positive return length. The values listed below were computed from the first return of the initial state and serve as a small-parameter validation of the modular behavior discussed above.
Table 2 gives \(hJ_m^1(k,2)\) for \(2\leq m \leq 10\) and \(2\leq k\leq 7\). The data show that the observed return lengths vary substantially with both \(m\) and \(k\) and need not behave monotonically. This variability is important later, because it indicates that the effective exponent space induced by the recurrence may differ considerably across parameter choices even for small moduli.
| \(m\) | \(hJ_m^1(2,2)\) | \(hJ_m^1(3,2)\) | \(h J_m^1(4, 2)\) | \(hJ_m^1(5,2)\) | \(hJ_m^1(6,2)\) | \(hJ_m^1(7,2)\) |
|---|---|---|---|---|---|---|
| \(2\) | \(3\) | \(7\) | \(3\) | \(7\) | \(3\) | \(7\) |
| \(3\) | \(13\) | \(8\) | \(4\) | \(13\) | \(8\) | \(4\) |
| \(4\) | \(6\) | \(14\) | \(6\) | \(14\) | \(6\) | \(14\) |
| \(5\) | \(8\) | \(5\) | \(31\) | \(20\) | \(31\) | \(8\) |
| \(6\) | \(39\) | \(56\) | \(12\) | \(51\) | \(24\) | \(28\) |
| \(7\) | \(57\) | \(42\) | \(48\) | \(8\) | \(21\) | \(16\) |
| \(8\) | \(12\) | \(32\) | \(12\) | \(28\) | \(12\) | \(28\) |
| \(9\) | \(39\) | \(24\) | \(12\) | \(39\) | \(24\) | \(12\) |
| \(10\) | \(24\) | \(35\) | \(93\) | \(140\) | \(93\) | \(56\) |
Lemma 2.3. Assume that \(hJ_m^p(k,t)\) is the least positive return length of the initial state modulo \(m\). Then for integers \(s,~n\) and \(m\geq 2\), we have
(i) \(J_{hJ_m^p(k,t)+n}^p(k,t) \equiv J_{n}^p(k,t) \ (\mathrm{mod}\ m)\),
(ii) \(J_{s\times(hJ_m^p(k,t))+n}^p(k,t) \equiv J_{n}^p(k,t) \ (\mathrm{mod}\ m)\).
Proof. Part (i) follows directly from the definition of \(hJ_m^p(k,t)\). For Part (ii), we have \[\begin{aligned} J_{s\times(hJ_m^p(k,t))+n}^p(k,t) \equiv & J_{(hJ_m^p(k,t))+(s-1)\times(hJ_m^p(k,t))+n}(k,t)\\ \equiv& J_{(s-1)(hJ_m^p(k,t))+n}^p(k,t)\\ \equiv& \vdots \\ \equiv& J_{n}^p(k,t) \ (\mathrm{mod}\ m), \end{aligned}\] which gives the result. ◻
Lemma 2.4. Assume that \(hJ_m^p(k,t)\) exists. Let \(n\) be an integer and \(m \geq 2\) be a positive number. If \[\left \{ \begin{array}{ll} J_n^p(k,t)\equiv 0& \ (\mathrm{mod}\ m),\\ J_{n+1}^p(k,t)\equiv 0& \ (\mathrm{mod}\ m),\\ \vdots\\ J_{n+t+p-2}^p(k,t)\equiv 0& \ (\mathrm{mod}\ m),\\ J_{n+t+p-1}^p(k,t)\equiv 0& \ (\mathrm{mod}\ m),\\ J_{n+t+p}^p(k,t)\equiv 1& \ (\mathrm{mod}\ m), \end{array}\right.\] then \(hJ_m^p(k,t) \mid n\).
Proof. There exists \(0 \leq i \leq hJ_m^p(k,t)\) such that \(n=t\times(hJ_m^p(k,t))+i\). Then for all \(0\leq j \leq t+p\), \(J_{n+j}^p(k,t)\equiv J_{i+j}^p(k,t) \ (\mathrm{mod}\ m)\), we have \[\left \{ \begin{array}{ll} J_i^p(k,t)\equiv 0& \ (\mathrm{mod}\ m),\\ J_{i+1}^p(k,t)\equiv 0& \ (\mathrm{mod}\ m),\\ \vdots\\ J_{i+t+p-2}^p(k,t)\equiv 0& \ (\mathrm{mod}\ m),\\ J_{i+t+p-1}^p(k,t)\equiv 0& \ (\mathrm{mod}\ m),\\ J_{i+t+p}^p(k,t)\equiv 1& \ (\mathrm{mod}\ m). \end{array}\right.\]
Thus, \(i\) is a period of the generalized \((k,t)\)-Jacobsthal \(p\)-numbers modulo \(m\) so \(hJ_m^p(k,t) \mid i\). Since \(0\leq i< hJ_m^p(k,t)\), we have that \(i=0\), and the result follows. ◻
We now define the generalized \((k,t)\)-Jacobsthal \(p\)-numbers in a finite group and examine the periodic behavior induced by the finite-state recurrence. We then specialize the construction to \(G_m\) and \(H_{(t,l,m)}\), where explicit normal forms make it possible to write the sequence terms in closed algebraic form.
Definition 3.1. For integers \(k\geq 1\), \(p \geq 1\) and \(t\geq 2\), the generalized \((k,t)\)-Jacobsthal \(p\)-numbers in a finite group is a sequence of group elements \(x_0, x_1, \cdots, x_n, \cdots\) for which, given finite group generators \(X=\lbrace a_0,a_1,\cdots,a_j\rbrace\), the elements are \(x_0=a_0,~x_1=a_1,~\cdots,~x_{j}=a_j\) and \[x_n=\left \{ \begin{array}{ll} x_0x_1\cdots x_{n-3}x_{n-2}^2x_{n-1}^k, & \mbox{for } j<n <t+p,\\ x_{n-p-t}\cdots x_{n-p-2}x_{n-p-1}^2x_{n-1}^k,& \mbox{for } n\geq p+t. \end{array}\right. \tag{4}\]
The \((k,t)\)-Jacobsthal \(p\)-numbers in a group are denoted by \(Q_p^{k,t}(G,X)\) and the corresponding sequence period is denoted by \(JQ_p^{k,t}(G,X)\).
Theorem 3.2. The generalized \((k,t)\)-Jacobsthal \(p\)-numbers in a finite group are eventually periodic. If the initial generator tuple reappears, the resulting sequence is purely periodic.
Proof.Let \(G\) be a finite group with \(|G|=m\). The recurrence in Definition 3.1 is determined by the current \((t+p)\)-tuple of consecutive group elements. Since there are only \(m^{t+p}\) such tuples, the infinite sequence generated by \(Q_p^{k,t}(G,X)\) must contain a repeated state. Once a state repeats, the determinism of the recurrence implies that all subsequent states repeat as well. Hence the sequence is eventually periodic. If one of the repeated states is the initial generator tuple \((x_0,x_1,\ldots,x_{t+p-1})\), then the sequence is purely periodic from the beginning. ◻
For \(m \in \mathbb{N}\), consider the finitely presented group \(G_m\) given by \[G_m=<a,b|a^{m}=b^m=1, [a,b]^a=[a,b],[a,b]^b=[a,b]>, m\geq 2.\]
Lemma 3.3. [9]Every element of \(G_m\) may be uniquely presented by \(a^rb^s[a,b]^t\) where \(0 \leq r, s, t \leq m-1\), and \(\mid G_m \mid= m^3\).
For \(p=1\) and \(t=2\), we define the sequences \(U_n(2)\) and \(w_{n}(2)\) as follows \[\begin{aligned} U_0(2)=&1,\\ U_1(2)=&0,\\ U_2(2)=&2,\\ U_n(2)=&U_{n-3}(2)+2U_{n-2}(2)+2U_{n-1}(2),~~n\geq 3.\\ w_{0}(2)=&w_{1}(2)=w_{2}(2)=0,\\ w_{n}(2)=&w_{n-3}(2)+2w_{n-2}(2)+2w_{n-1}(2)-(U_{n-2}(2)J_{n-1}^1(2,2)+(J_{n-1}^1(2,2)\\ &+J_{n}^1(2,2))U_{n-2}(2)+(J_{n-1}^1(2,2)+2J_{n}^1(2,2))U_{n-1}(2)\\ &+(J_{n-1}^1(2,2) +2J_{n}^1(2,2)+J_{n+1}^1(2,2))U_{n-1}(2)), ~n\geq 3. \end{aligned}\]
Lemma 3.4. Every element of \(Q_1^{2,2}(G_m,X)\) can be expressed
as
\(x_n=a^{U_{n}(2)}b^{J_{n+2}^1(2,2)}[a,b]^{w_{n}(2)}\), \(n\geq 3\).
Proof. For \(n=2\) and \(n=3\), we have \(x_2=x_0^2x_1^2=a^2b^2\) and \(x_3=x_0x_1^2x_2^2=a^5b^6[a,b]^{-12}\), respectively. Then by induction on \(n\), we have \[\begin{aligned} &x_n=x_{n-3}(x_{n-2})^2(x_{n-1})^2\\ &=a^{U_{n-3}(2)}b^{J_{n-1}^1(2,2)}[a,b]^{w_{n-3}(2)}(a^{U_{n-2}(2)}b^{J_{n}^1(2,2)[a,b]^{w_{n-2}(2)}})^2(a^{U_{n-1}(2)}b^{J_{n+1}^1(2,2)[a,b]^{w_{n-1}(2)}})^2\\ &=a^{U_{n-3}(2)+U_{n-2}(2)}b^{J_{n-1}^1(2,2)+J_{n}^1(2,2)}[a,b]^{w_{n-3}(2)+w_{n-2}(2)-U_{n-2}(2)J_{n-1}^1(2,2)}a^{U_{n-2}(2)}b^{J_{n}^1(2,2)[a,b]^{w_{n-2}(2)}}\\ &~~~~(a^{U_{n-1}(2)}b^{J_{n+1}^1(2,2)[a,b]^{w_{n-1}(2)}})^2\\ &=\cdots\\ &=a^{U_{n-3}(2)+2U_{n-2}(2)+2U_{n-1}(2)}b^{J_{n+2}^1(2,2)}\\ &~~~~[a,b]^{w_{n-3}(2)+2w_{n-2}(2)+2w_{n-1}(2)-(U_{n-2}(2)J_{n-1}^1(2,2)+(J_{n-1}^1(2,2)+J_{n}^1(2,2))U_{n-2}(2)+(J_{n-1}^1(2,2)+2J_{n}^1(2,2))U_{n-1}(2)}\\ &~~~~[a,b]^{-(J_{n-1}^1(2,2)+2J_{n}^1(2,2)+J_{n+1}^1(2,2))U_{n-1}(2)+\cdots+(J_{n-1}^1(2,2)+2J_{n}^1(2,2)+(2-1)J_{n+1}^1(2,2))U_{n-1}(2))}\\ &=a^{U_{n}(2)}b^{J_{n+2}^1(2,2)}[a,b]^{w_{n}(2)}, \end{aligned}\] and the assertion holds. ◻
For \(p=1\) and \(t=2\), we define the sequences \(U_n(k)\) and \(w_{n}(k)\) as follows \[\begin{aligned} U_0(k)=&1,\\ U_1(k)=&0,\\ U_2(k)=&2,\\ U_n(k)=&U_{n-3}(k)+2U_{n-2}(k)+kU_{n-1}(k),~~n\geq 3.\\ w_{0}(k)=&w_{1}(k)=w_{2}(k)=0,\\ w_{n}(k)=&w_{n-3}(k)+2w_{n-2}(k)+kw_{n-1} (k)-(U_{n-2}(k)J_{n-1}^1(k,2)+(J_{n-1}^1(k,2)\\ &+J_{n}^1(k,2))U_{n-2}(k)+(J_{n-1}^1(k,2)+2J_{n}^1(k,2))U_{n-1}(k) +(J_{n-1}^1(k,2)+2J_{n}^1(k,2)\\ &+J_{n+1}^1(k,2))U_{n-1}(k)+\cdots+(J_{n-1}^1(k,2)+2J_{n}^1(k,2)\\ &+(k-1)J_{n+1}^1(k,2))U_{n-1}(k)), ~n\geq 3. \end{aligned}\]
Lemma 3.5. Every element of \(Q_1^{k,2}(G_m,X)\) can be expressed as \[x_n=a^{U_{n}(k)}b^{J_{n+2}^1(k,2)}[a,b]^{w_{n}(k)},\quad~n\geq 3.\]
Proof. For \(n=2\), we have \(x_2=x_0^2x_1^k=a^2b^k\). Then by induction on \(n\), we have \[\begin{aligned} x_n&=x_{n-3}(x_{n-2})^2(x_{n-1})^k\\ &=a^{U_{n-3}(k)}b^{J_{n-1}^1(k,2)}[a,b]^{w_{n-3}(k)}(a^{U_{n-2}(k)}b^{J_{n}^1(k,2)[a,b]^{w_{n-2}(k)}})^2(a^{U_{n-1}(k)}b^{J_{n+1}^1(k,2)[a,b]^{w_{n-1}(k)}})^k\\ &=a^{U_{n-3}(k)+U_{n-2}(k)}b^{J_{n-1}^1(k,2)+J_{n}^1(k,2)}[a,b]^{w_{n-3}(k)+w_{n-2}(k)-U_{n-2}(k)J_{n-1}^1(k,2)}a^{U_{n-2}(k)}\\&~~~~b^{J_{n}^1(k,2)[a,b]^{w_{n-2}(k)}} (a^{U_{n-1}(k)}b^{J_{n+1}^1(k,2)[a,b]^{w_{n-1}(k)}})^k\\ &=\cdots\\ &=a^{U_{n-3}(k)+2U_{n-2}(k)+kU_{n-1}(k)}b^{J_{n+2}^1(k,2)}\\ &~~~~[a,b]^{w_{n-3}(k)+2w_{n-2}(k)+kw_{n-1} (k)-(U_{n-2}(k)J_{n-1}^1(k,2)+(J_{n-1}^1(k,2)+J_{n}^1(k,2))U_{n-2}(k)}\\ &~~~~[a,b]^{+(J_{n-1}^1(k,2)+2J_{n}^1(k,2))U_{n-1}(k) +(J_{n-1}^1(k,2)+2J_{n}^1(k,2)+J_{n+1}^1(k,2))U_{n-1}(k)}\\ &~~~~[a,b]^{+\cdots+(J_{n-1}^1(k,2)+2J_{n}^1(k,2)+(k-1)J_{n+1}^1(k,2))U_{n-1}(k))}\\ &=a^{U_{n}(k)}b^{J_{n+2}^1(k,2)}[a,b]^{w_{n}(k)}, \end{aligned}\] and the assertion holds. ◻
Lemma 3.6. If \(JQ_1^{k,2}(G_m,X)=s\), then \(s\) is the least integer such that \[\left \{ \begin{array}{ll} U_n(k)\equiv 1& \ (\mathrm{mod}\ m),\\ U_{n+1}(k) \equiv 0& \ (\mathrm{mod}\ m),\\ U_{n+2}(k) \equiv 2& \ (\mathrm{mod}\ m),\\ J_{n+2}^1(k,2)\equiv 0& \ (\mathrm{mod}\ m),\\ J_{n+3}^1(k,2) \equiv 1& \ (\mathrm{mod}\ m),\\ J_{n+4}^1(k,2)\equiv k& \ (\mathrm{mod}\ m),\\ w_n(k)\equiv 0& \ (\mathrm{mod}\ m),\\ w_{n+1}(k)\equiv 0& \ (\mathrm{mod}\ m),\\ w_{n+2}(k)\equiv 0& \ (\mathrm{mod}\ m), \end{array}\right.\] hold. Further, \(hJ_m^1(k,2)\mid JQ_1^{k,2}(G_m,X)\).
Proof. By Lemma 3.3, we obtain that \(x_n=a^{U_{n}(k)}b^{J_{n+2}^1(k,2)}[a,b]^{w_{n}(k)}\). Since \(x_s=a\), \(x_{s+1}=b\) and \(x_{s+2}=a^2b^k\), by the defining initial conditions we have \[\left \{ \begin{array}{ll} U_s(k)\equiv 1& \ (\mathrm{mod}\ m),\\ U_{s+1}(k) \equiv 0& \ (\mathrm{mod}\ m),\\ U_{s+2}(k) \equiv 2& \ (\mathrm{mod}\ m),\\ J_{s+2}^1(k,2)\equiv 0& \ (\mathrm{mod}\ m),\\ J_{s+3}^1(k,2) \equiv 1& \ (\mathrm{mod}\ m),\\ J_{s+4}^1(k,2)\equiv k& \ (\mathrm{mod}\ m),\\ w_s(k)\equiv 0& \ (\mathrm{mod}\ m),\\ w_{s+1}(k)\equiv 0& \ (\mathrm{mod}\ m),\\ w_{s+2}(k)\equiv 0& \ (\mathrm{mod}\ m). \end{array}\right.\] Then Lemma 2.4 gives that \(hJ_m^1(k,2) \mid JQ_1^{k,2}(G_m,X)\). ◻
For \(t,l,m \in \mathbb{N}\), consider the Heisenberg group \(H_{(t,l,m)}\) given by \[H_{(t,l,m)}=<a,b, c|a^{t}=b^l=c^m=1, [a,b]=c, [a,c]=[b,c]=1>.\]
Lemma 3.7. [22]Element \(H_{(t,l,m)}\) of the Heisenberg group can be written uniquely in the form \(a^i b^j c^k\) where \(0 \leq i \leq t-1, 0 \leq j \leq l-1\) and \(0 \leq k \leq m-1\).
For \(p=1\) and \(t=2\), define the sequences \(T_n(2)\) and \(g_{n}(2)\) as follows \[\begin{aligned} T_0(2)=&0,\\ T_1(2)=&1,\\ T_2(2)=&0,\\ T_n(2)=&T_{n-3}(2)+2T_{n-2}(2)+2T_{n-1}(2),~~n\geq 3.\\ g_{0}(2)=&g_{1}(2)=0, g_{2}(2)=1,\\ g_{n}(2)=&g_{n-3}(2)+2g_{n-2}(2)+2g_{n-1}(2)-(T_{n-3}(2)J_{n-4}^1(2,2)+(T_{n-3}(2)+T_{n-2}(2))J_{n-4}^1(2,2)\\ &+(T_{n-3}(2)+2T_{n-2}(2))J_{n-3}^1(2,2)+(T_{n-3}(2)+2T_{n-2}(2)\\ &+T_{n-1}(2))J_{n-3}^1(2,2)), n\geq 3. \end{aligned}\]
Lemma 3.8. Every element of \(Q_1^{2,2}(H_{(t,l,m)},X)\) can be expressed as \(x_n=a^{J_{n-2}^1(2,2)}b^{T_{n}(2)}c^{g_{n}(2)}\), \(n\geq 3\).
Proof. For \(n=3\) and \(n=4\), we have \(x_3=x_0x_1^2x_2^2=ab^2c^2\) and \(x_4=x_1x_2^2x_3^2=a^6b^{14}c^{-19}\), respectively. Then by induction on \(n\), we have \[\begin{aligned} x_n&=x_{n-3}(x_{n-2})^2(x_{n-1})^2\\ &=a^{J_{n-5}^1(2,2)}b^{T_{n-3}(2)}c^{g_{n-3}(2)} (a^{J_{n-4}^1(2,2)}b^{T_{n-2}(2)}c^{g_{n-2}(2)})^2(a^{J_{n-3}^1(2,2)}b^{T_{n-1}(2)}c^{g_{n-1}(2)})^2\\ &=a^{J_{n-5}^1(2,2)+J_{n-4}^1(2,2)}b^{T_{n-3}(2)+T_{n-2}(2)}c^{g_{n-3}(2)+g_{n-2}(2)-(T_{n-3}(2)J_{n-4}^1(2,2))}a^{J_{n-4}^1(2,2)}\\ &~~~~b^{T_{n-2}(2)}c^{g_{n-2}(2)}(a^{J_{n-4}^1(2,2)}b^{T_{n-1}(2)}c^{g_{n-1}(2)})^2\\ &=a^{J_{n-5}^1(2,2)+2J_{n-4}^1(2,2)}b^{T_{n-3}(2)+2T_{n-2}(2)}\\ &~~~~c^{g_{n-3}(2)+2g_{n-2}(2)-(T_{n-3}(2)J_{n-4}^1(2,2)+(T_{n-3}(2)+T_{n-2}(2))J_{n-4}^1(2,2))}\\ &~~~~(a^{J_{n-3}^1}(2,2)b^{T_{n-1}(2)}c^{g_{n-1}(2)})^2\\ &=\cdots\\ &=a^{J_{n-2}^1(2,2)}b^{T_{n}(2)}c^{g_{n-3}(2)+2g_{n-2}(2)+2g_{n-1} (2)}c^{-(T_{n-3}(2)J_{n-4}^1(2,2)+(T_{n-3}(2)}\\ &~~~~\times c^{T_{n-2}(2))J_{n-4}^1(2,2) +(T_{n-3}(2)+2T_{n-2}(2))J_{n-3}^1(2,2)+(T_{n-3}(2)+2T_{n-2}(2)+T_{n-1}(2))J_{n-3}^1(2,2))}\\ &=a^{J_{n-2}^1(2,2)}b^{T_{n}(2)}c^{g_{n}(2)}, \end{aligned}\] and the assertion holds. ◻
For \(p=1\) and \(t=2\), we define the sequences \(T_n(2)\) and \(g_{n}(2)\) as follows \[\begin{aligned} T_0(k)=&0,\\T_1(k)=&1,\\T_2(k)=&0,\\ T_n(k)=&T_{n-3}(k)+2T_{n-2}(k)+kT_{n-1}(k),~~n\geq 3.\\ g_{0}(k)=&g_{1}(k)=0,\\ g_{2}(k)=&1,\\ g_{n}(k)=&g_{n-3}(k)+2g_{n-2}(k)+kg_{n-1}(k)-(T_{n-3}(k)J_{n-4}^1(k,2)+(T_{n-3}(k)\\ &+T_{n-2}(k))J_{n-4}^1(k,2)+(T_{n-3}(k)+2T_{n-2}(k))J_{n-3}^1(k,2)\\ &+(T_{n-3}(k)+2T_{n-2}(k)+T_{n-1}(k))J_{n-3}^1(k,2)+(T_{n-3}(k)+2T_{n-2}(k)\\ &+2T_{n-1}(k))J_{n-3}^1(k,2) +\cdots+(T_{n-3}(k)+2T_{n-2}(k)\\&+(k-1)T_{n-1}(k))J_{n-3}^1(k,2)),~~n\geq 3. \end{aligned}\]
The proof of the following lemma is similar to that for Lemma 3.6 and so is omitted.
Lemma 3.9. Every element of \(Q_1^{k,2}(H_{(t,l,m)},X)\) can be expressed as \(x_n=a^{J_{n-2}^1(k,2)}b^{T_{n}(k)}c^{g_{n}(k)}\), \(n\geq 3\).
Lemma 3.10. If \(JQ_1^{k,2}(H_{(t,l,m)},X)=i\), then \(i\) is the least integer such that \[\left \{ \begin{array}{ll} J_{n-2}^1(k,2)\equiv 1& \ (\mathrm{mod}\ t),\\ J_{n-1}^1(k,2)\equiv 0& \ (\mathrm{mod}\ t),\\ J_{n}^1(k,2)\equiv 0& \ (\mathrm{mod}\ t),\\ T_n(k)\equiv 0& \ (\mathrm{mod}\ l),\\ T_{n+1}(k)\equiv 1& \ (\mathrm{mod}\ l),\\ T_{n+2}(k)\equiv 0& \ (\mathrm{mod}\ l),\\ g_n(k)\equiv 0& \ (\mathrm{mod}\ m),\\ g_{n+1}(k)\equiv 0& \ (\mathrm{mod}\ m),\\ g_{n+2}(k)\equiv 1& \ (\mathrm{mod}\ m),\\ \end{array}\right.\] holds. Moreover, \(hJ_t^1(k,2) \mid JQ_1^{k,2}(H_{(t,l,m)},X)\).
Proof. By Lemma 3.7, we obtain that \(x_n=a^{J_{n-2}^1(k,2)}b^{T_{n}(k)}c^{g_{n}(k)}\). Since \(x_i=a\), \(x_{i+1}=b\) and \(x_{i+2}=c\), the explicit representation above yields \[\left \{ \begin{array}{ll} J_{i-2}^1(k,2)\equiv 1& \ (\mathrm{mod}\ t),\\ J_{i-1}^1(k,2)\equiv 0& \ (\mathrm{mod}\ t),\\ J_{i}^1(k,2)\equiv 0& \ (\mathrm{mod}\ t),\\ T_i(k)\equiv 0& \ (\mathrm{mod}\ l),\\ T_{i+1}(k)\equiv 1& \ (\mathrm{mod}\ l),\\ T_{i+2}(k)\equiv 0& \ (\mathrm{mod}\ l),\\ g_i(k)\equiv 0& \ (\mathrm{mod}\ m),\\ g_{i+1}(k)\equiv 0& \ (\mathrm{mod}\ m),\\ g_{i+2}(k)\equiv 1& \ (\mathrm{mod}\ m).\\ \end{array}\right.\] Then from the return condition encoded in the displayed congruences, \[hJ_t^1(k,2)\mid JQ_1^{k,2}(H_{(t,l,m)},X).\] ◻
In this section, we present two Massey–Omura-type encryption algorithms based on generalized Jacobsthal exponent families. The emphasis here is on algebraic correctness rather than on claiming a security advantage over the classical protocol.
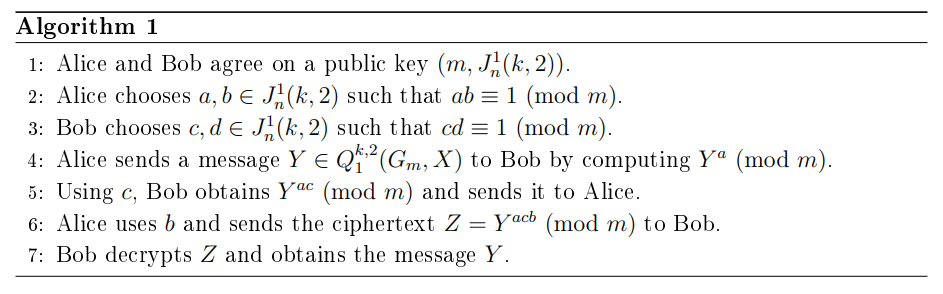
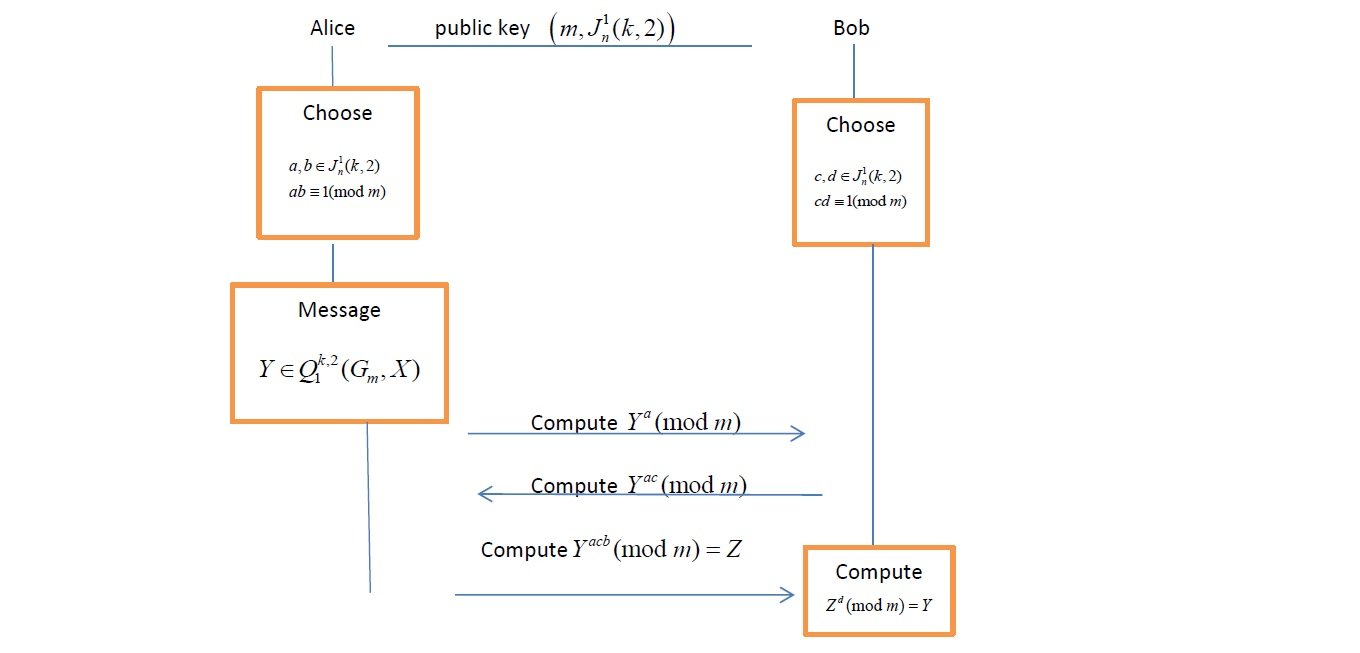
Alice and Bob first agree on public parameters \((m,J_n^1(k,2))\). They then choose exponents \(a,b,c,d\) from the Jacobsthal-derived set so that \(ab\equiv 1 \ (\mathrm{mod}\ m)\) and \(cd\equiv 1 \ (\mathrm{mod}\ m)\). In other words, the admissible exponents are restricted to sequence values that satisfy the invertibility condition required by the three-pass protocol. In Algorithm 1, the message space is \(Q_1^{k,2}(G_m,X)\). Alice sends a message \(Y\in Q_1^{k,2}(G_m,X)\) to Bob by computing \(Y^a \ (\mathrm{mod}\ m)\), Bob returns \(Y^{ac} \ (\mathrm{mod}\ m)\), and Alice then uses \(b\) to obtain \(Z=Y^{acb}\equiv Y^c \ (\mathrm{mod}\ m)\). Bob finally decrypts with \(d\) and recovers \(Y\) because \(cd\equiv 1 \ (\mathrm{mod}\ m)\). All computations are performed in the relevant group using the normal form with exponents reduced modulo \(m\). The algorithm steps are given in Algorithm 1 and illustrated in Figure 1.
Lemma 4.1. The original message \(Y\) is obtained by Bob after decrypting the ciphertext \(Z\).
Proof. We show that \(Z^d=Y\). We have that \[Z=(Y^{ac})^b\equiv Y^{acb} \ (\mathrm{mod}\ m).\]
Using \(ab\equiv 1 \ (\mathrm{mod}\ m)\), we obtain \(Z=Y^c \ (\mathrm{mod}\ m)\), and Bob decrypts using \(d\). Since \(Y \in Q_1^{k,2}(G_m,X)\), Lemma 3.3 and the fact that \(cd\equiv 1 \ (\mathrm{mod}\ m)\) give \[Z^d=Y^{cd}\equiv Y \ (\mathrm{mod}\ m).\] ◻
Consider the following example.
Example 4.2. Let \(p=1, t=2\) and \(k=2\).
Alice and Bob agree on a public key \((7,J_n^1(2,2) )\).
Alice chooses \(a:=J_4^1(2,2)=2\) and \(b:=J_{14}^1(2,2)=70032\) such that \(ab\equiv 1 \ (\mathrm{mod}\ 7)\).
Bob chooses \(c:=J_6^1(2,2)=3\) and \(d:=J_{10}^1(2,2)=1090\) such that \(cd\equiv 1 \ (\mathrm{mod}\ 7)\).
Alice sends the message \(Y=a^5b^6[a,b]^2\in Q_1^{2,2}(G_m,X)\) to Bob by computing \((a^5b^6[a,b]^2)^2=(a^5b^6[a,b]^2)(a^5b^6[a,b]^2)=a^{10}b^{12}[a,b]^{-26}\equiv a^3b^5[a,b]^2 \ (\mathrm{mod}\ 7)\).
Using \(c\), Bob obtains \((a^3b^5[a,b]^2)^3=a^2b^1[a,b]^3 \ (\mathrm{mod}\ 7)\) and sends it to Alice.
Using \(b\), Alice sends the ciphertext \(Z=(a^2b^1[a,b]^3)^{70032}=ab^4 \ (\mathrm{mod}\ 7)\) to Bob.
Bob decrypts \(Z\) as \(Z^{1090}=(ab^4)^{1090} :=a^5b^6[a,b]^2 \ (\mathrm{mod}\ 7)\) and obtains the message \(Y\).
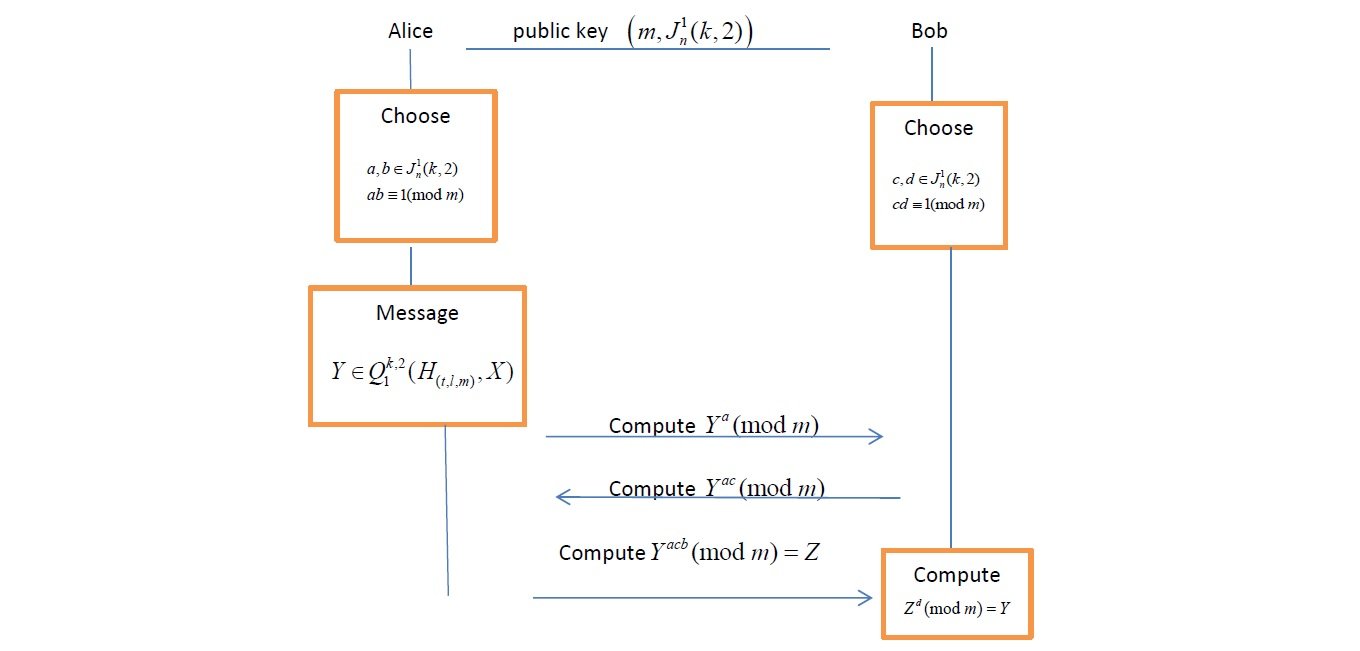
Consider the Heisenberg group \(H_{(t,l,m)}\) and suppose that \(t=l=m\). Algorithm 2 is similar to Algorithm 1 but \(Q_1^{k,2}(H_{(t,m,l)},X)\) is used for the message.
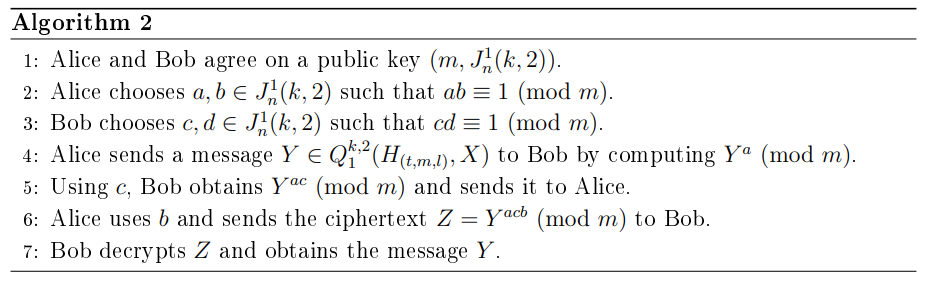
The algorithm steps are illustrated in Figure 2. In this algorithm, the message \(Y\) is obtained by Bob after decrypting the ciphertext \(Z\). Since the verification is analogous to that of Lemma 4.1, we record the argument below only for completeness.
Lemma 4.3. The original message \(Y\) is obtained by Bob after decrypting the ciphertext \(Z\).
Proof. We show that \(Z^d=Y\). We have that \[Z=(Y^{ac})^b\equiv Y^{acb} \ (\mathrm{mod}\ m).\]
Using \(ab\equiv 1 \ (\mathrm{mod}\ m)\), we obtain \(Z=Y^c \ (\mathrm{mod}\ m)\), and Bob decrypts using \(d\). Since \(Y \in Q_1^{k,2}(H_{(t,m,l)},X)\), Lemma 3.7 and the fact that \(cd\equiv 1 \ (\mathrm{mod}\ m)\) give \[Z^d=Y^{cd}\equiv Y \ (\mathrm{mod}\ m).\] ◻
Consider the following example.
Example 4.4. Let \(p=1, t=2\) and \(k=2\).
Alice and Bob agree on a public key \((5, J_n^1(2,2) )\).
Alice chooses \(a:=J_{6}^1(2,2)=17\) and \(b:=J_{7}^1(2,2)=48\) such that \(ab\equiv 1 \ (\mathrm{mod}\ 5)\).
Bob chooses \(c:=J_{14}^1(2,2)=70032\) and \(d:=J_{15}^1(2,2)=198273\) such that \(cd\equiv 1 \ (\mathrm{mod}\ 5)\).
Alice sends a message \(Y=ab^2c^2\in Q_1^{2,2}(H_{(t,m,l)},X)\) to Bob by computing \((ab^2c^2)^{17}\equiv a^2b^4c^2 \ (\mathrm{mod}\ 5)\).
Using \(c\), Bob obtains \((a^2b^4c^2)^{70032}\equiv a^4b^3c \ (\mathrm{mod}\ 5)\) and sends it to Alice.
Using \(b\), Alice sends the ciphertext \(Z=(a^4b^3c)^{48}\equiv a^2b^4c^2 \ (\mathrm{mod}\ 5)\) to Bob.
Bob decrypts \(Z\) as \(Z^{198273}=(a^2b^4c^2)^{198273}\equiv ab^2c^2 \ (\mathrm{mod}\ 5)\) and obtains the message \(Y\).
This section discusses the security-related aspects of the proposed constructions. We emphasize that the primary contribution of this work is algebraic and structural, rather than the establishment of a cryptosystem with modern, provable security guarantees. Accordingly, the discussion is framed to clarify correctness, assumptions, and limitations, and to position the proposed schemes as mathematically motivated variants of the classical Massey-Omura protocol.
The proposed constructions should be understood as algebraic variants of the classical Massey-Omura protocol, rather than as replacements or improvements in a security-theoretic sense. While the use of structured exponent sequences introduces novel mathematical behavior, no claim is made that the resulting schemes provide stronger security guarantees than the original Massey–Omura protocol. Any comparisons are limited to algebraic structure and correctness properties, and not to resistance against cryptanalytic attacks. We now consider attacks on the proposed Massey-Omura encryption with the generalized \((k,t)\)-Jacobsthal \(p\)-numbers and compare it with the original Massey-Omura encryption. The original Massey–Omura encryption is implemented in \(\mathbb{Z}_p^{\ast}\), so Alice chooses private exponents \(e_A,d_A\) such that \(e_Ad_A\equiv 1 \ (\mathrm{mod}\ p-1)\) and Bob chooses private exponents \(e_B,d_B\) such that \(e_Bd_B\equiv 1 \ (\mathrm{mod}\ p-1)\). Thus the admissible exponents are units modulo \(p-1\), and their number is \(\varphi(p-1)\). In the proposed construction, Alice selects \(a\) and \(b\) from values of \(J_n^p(k,t)\) satisfying \(ab\equiv 1 \ (\mathrm{mod}\ m)\), while Bob selects \(c\) and \(d\) satisfying \(cd\equiv 1 \ (\mathrm{mod}\ m)\). The crucial difference is therefore not the logical structure of the three-pass protocol, but the restriction of the exponent set to a recurrence-defined family that must still satisfy the same invertibility requirement.
The security considerations of the proposed constructions are analyzed within the same conceptual framework as the classical Massey–Omura three-pass protocol. In this setting, the communication channel is assumed to be observable, and an adversary may obtain all transmitted group elements exchanged between legitimate parties. The purpose of this work is not to introduce a new adversarial model or to redefine security notions, but rather to study the algebraic behavior and correctness of Massey-Omura-type protocols when private exponents are selected from structured recurrence-based sequences. Accordingly, the analysis focuses on algebraic feasibility, invertibility conditions, and the preservation of the protocol’s functional properties under such constraints.
As in the classical Massey-Omura protocol, the security intuition underlying the proposed schemes relies on the assumed hardness of the discrete logarithm problem (DLP) in the chosen platform group. Specifically, given a group element \(g\) and an exponentiated element \(g^x\), it is assumed to be computationally infeasible for a passive adversary to recover \(x\) without additional information. The present work does not introduce new computational hardness assumptions beyond this classical setting. However, it is important to note that the constructions employ finite groups with specific algebraic structure, including nilpotent and class-\(2\) groups. From a security perspective, both approaches rely on exponentiation in finite groups and do not introduce fundamentally different hardness assumptions. The structured nature of the Jacobsthal-based exponent selection primarily affects the algebraic form and distribution of admissible keys rather than the underlying attack model. No claim is made that the structured key selection provides increased resistance to cryptanalytic attacks compared to the classical setting. Instead, the contribution of the proposed schemes lies in demonstrating that Massey-Omura encryption can be realized using recurrence-defined exponent sequences in finite groups while preserving functional correctness and algebraic feasibility. The resulting constructions thus extend the classical protocol framework in an algebraic direction without altering its foundational security assumptions.
Although the defining sequences are infinite over the integers, all cryptographic operations take place in finite groups or modulo finite integers. As a result, the induced exponent sequences are periodic on a finite state space, and the effective cryptographic keyspace is finite. The infinitude of the underlying integer sequence therefore does not imply an infinite cryptographic keyspace. Instead, the security-relevant parameters are determined by the order or exponent of the underlying group, the period of the recurrence modulo the relevant modulus, and the subset of sequence values satisfying the required invertibility conditions. The variability already visible in Table 2 provides a small computational illustration of this point. We now analyze the computational hardness of recovering private exponents or plaintexts from the publicly transmitted values in the proposed Massey–Omura-type protocols. As in the classical three-pass protocol, a passive adversary observes the values \(Y^{a}\), \(Y^{ac}\), and \(Y^{acb}\), all lying in \(G\), where \(G\) is either \(G_{m}\) or \(H(t,\ell,m)\). The security of the scheme therefore depends on the difficulty of recovering exponents from group exponentiation and on the effective size of the exponent space induced by the generalized \((k,t)\)-Jacobsthal \(p\)-numbers.
Let \(g \in G\) be a group generator and suppose an adversary attempts to recover the exponent \(a\) from \(g^{a}\). In general, nilpotent groups of class 2, the discrete logarithm problem (DLP) does not have known polynomial-time solutions, and the best generic attacks (e.g., adaptations of Pollard’s rho or baby-step/giant-step) run in time \(O(\sqrt{|G|})\). Thus, if exponents were chosen uniformly, recovering \(a\) or \(c\) would require \(O(\sqrt{m})\) group operations. Since the proposed scheme preserves the same exponentiation structure as the classical Massey-Omura protocol, it inherits this attack complexity provided that the exponent space is sufficiently large.
In the present construction, private exponents are not arbitrary residues modulo \(m\), but are selected from the generalized \((k,t)\)-Jacobsthal \(p\)-sequence reduced modulo \(m\). Because this sequence is ultimately periodic with period \(hJ_{m}^p(k,t)\), the total number of admissible exponents is at most \(\mathcal{K} = hJ_{m}^p(k,t)\). Therefore, an adversary needs to search only this set, and the cost of a brute-force exponent-recovery attack reduces to \(O\!\left(\sqrt{hJ_{m}^p(k,t)}\right)\). If \(hJ_{m}^p(k,t) \ll m\), then the effective exponent entropy is significantly reduced, and the protocol becomes easier to attack than the classical Massey-Omura scheme.
The recurrence defining the generalized Jacobsthal numbers has order \(t+p\), and its reduction modulo \(m\) is periodic. Although an upper bound on the maximum possible period is \(m^{\,t+p}\), the actual period may be much smaller for certain moduli, particularly those with small prime factors or special algebraic properties. If \(hJ_{m}^p(k,t) \text{ is small}\), then
\(\bullet\) the entropy of private exponents decreases to \(\log_{2}(hJ_{m}^p(k,t))\);
\(\bullet\) brute-force exponent enumeration may be feasible;
\(\bullet\) the protocol’s security degrades below that of the classical three-pass scheme.
Thus, periodicity plays a central role in the practical security of the proposed method.
To maintain security comparable to the classical Massey-Omura protocol, the parameters \((k,t,p,m)\) must be chosen so that the Jacobsthal period \(hJ_{m}^p(k,t)\) is large. In particular
\(\bullet\) the modulus \(m\) should avoid values known to induce short recurrence periods;
\(\bullet\) the recurrence order \(t+p\) should be sufficiently large to support long periods;
\(\bullet\) the actual period \(hJ_{m}^p(k,t)\) should be estimated or empirically validated for any proposed parameter set.
The computational cost of attacking the proposed schemes is dominated by exponent recovery. However, because exponents are drawn from periodic Jacobsthal sequences, the effective keyspace is \(hJ_{m}^p(k,t)\), not \(m\). Consequently, attack costs scale as \(O(\sqrt{hJ_{m}^p(k,t)})\), emphasizing the importance of ensuring that the Jacobsthal period is sufficiently large.
In this work, we introduced the generalized \((k,t)\)-Jacobsthal \(p\)-numbers and analyzed their structural properties in both integer and finite-group settings. We established modular periodicity results, derived recurrence relations for the induced group sequences, and extended the construction to the specific finite groups \(G_m\) and \(H(t,\ell,m)\). These algebraic foundations enabled the formulation of two Massey–Omura-type encryption mechanisms in which private exponents are drawn from recurrence-defined sequences rather than from unrestricted residue classes. We proved the correctness of the proposed schemes and clarified how periodicity controls both the feasibility of invertible exponent selection and the size of the effective keyspace. The contribution of the paper is therefore algebraic: it shows that structured exponent families arising from generalized Jacobsthal recurrences can be incorporated into three-pass protocols without changing the underlying security assumptions. At the same time, the analysis in Section 5 makes clear that the resulting constructions should be viewed as mathematically motivated variants of the classical Massey–Omura scheme, not as universally stronger replacements. Similar ideas may also be explored with other recurrence families, including Fibonacci- and Pell-type sequences on finite groups [8, 14, 15, 16], which may further illuminate the mathematical and practical implications of recurrence-based exponent selection in cryptographic protocols.
The authors declare that there are no conflicts of interest regarding the publication of this paper.